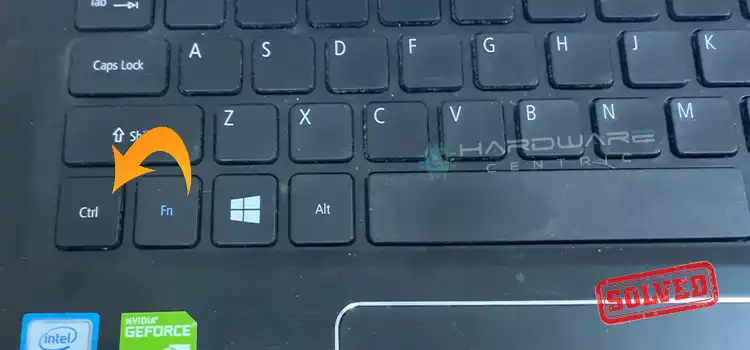
Left CTRL Key Not Working | How to Get Left CTRL Back in Track?
When working with text, documents, as well as other items on your computer, one of the most useful keys is the left control (Ctrl) key, which allows for a variety of shortcuts and alterations. Whenever the left Ctrl key stops working, that will be a very irritating situation because it can make it difficult for you…